Have you ever wondered how safe your intellectual property is when stored on your computer? We invited Paul Peters of the Cyber Resilience Centre for Wales to give us some tips on how we can help make our IP cyber-safe.
Intellectual property. It’s something you create with your mind. It could be the name of your product or brand, your invention, the design or look of your product, the things you write, make or produce.
For many companies these might be considered their most valuable assets…so how can you help prevent your IP from being accessed and used without your permission?
Definition
Hacker: a person who uses computers to gain unauthorised access to data.
Defining the hacker
Hackers go after whatever is considered valuable, whether that be access to data, the data itself, or the opportunity to take over an account and carry out a fraudulent transaction. Their business model is to disrupt and blackmail you into making a payment or to access your information.
Misappropriation of intellectual property is a real issue and can have a significant impact on a business. This can be in terms of financial cost but also reputation. You may have seen reports of hacking groups and state actors seeking to obtain sensitive information. This can include obtaining IP from a business, for example, confidential information about your invention. Poor cyber security has the potential to increase vulnerability to such an attack.

Definition
Cyber-attack: attempts to damage, disrupt or gain unauthorised access to computer systems, networks or devices.
Cyber breach: an incident in which data, computer systems or networks are accessed or affected in a non-authorised way.
So how can I help keep my business safe from a cyber-attack or cyber breach?
A cyber breach can give the attacker access to IT systems, which means they can access some of your most valuable information and assets. This can include your IP if you do not put in measures to protect yourself. The Cyber Resilience Centre for Wales is often asked by businesses how they can protect themselves.
These are some of the steps we recommend:
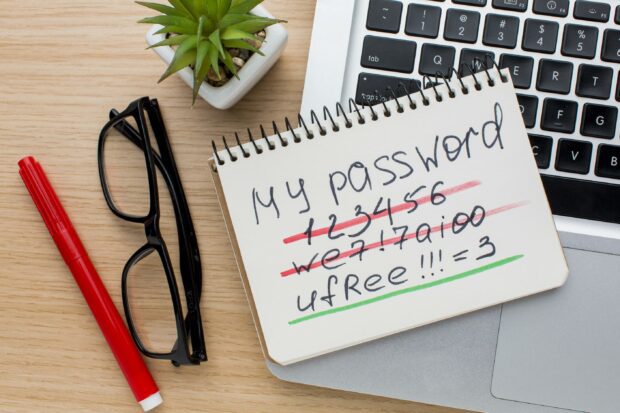
Use a strong password
There are many cases of intruders preying on weak employee passwords. Once they have cracked those accounts, getting into internal systems is easy. They can use existing accounts as though they are legitimate users, with their activity going unnoticed. The use of a strong password, ideally using three random words with capitals, symbols and numbers mixed in, makes the password far more difficult to crack.
One final step we recommend is using two-factor authentication (2FA) which can strengthen the security on your account considerably.

Definition
Phishing: the fraudulent practice of sending emails purporting to be from reputable companies in order to induce individuals to click on a link to reveal personal information, such as passwords and credit card numbers.
Identify ‘phishing’ emails
The most common threat currently used by cybercriminals is a ‘phishing’ email. This may be a general widespread attack, or a more focused assault on your organisation.
What happens when you click on a corrupt attachment or link?
This may allow malware (also known as malicious software) to be downloaded to your computer which could be used to:
- reveal your passwords
- access your email account
- send emails pretending to be you
- obtain client data and blackmail you for its return
The key to defending yourself against this attack is staff awareness. This will help all employees to understand the key elements to recognising a phishing email if or when they receive one. This will place your organisation in a far stronger position to prevent themselves falling victim to being hacked and blackmailed.

The principle of 'least privilege'
Misappropriation of IP can be an internal as well as an external threat. We recommend a tiering model for administrative accounts which allows employees access to the specific administrative capabilities they need, rather than all of them. This limits users on privileged accounts. It also reduces the access an attacker gains if a lower privilege administrator account is compromised.
If you need to share confidential information with others, we recommend asking them to sign a non-disclosure document (NDA). https://www.gov.uk/government/publications/non-disclosure-agreements

For more information on making your business cyber-safe:
- The National Cyber Resilience Centre network has regional centres across the uk who can help businesses improve their cyber safety through simple yet effective ways. Find your regional Cyber Resilience Centre through this link: Regional Centres - National CRC Group
- The Cyber Resilience Centre for Wales (WCRC) offers free core membership to help Wales-based businesses improve their cyber security. It takes just a matter of moments to sign up and receive regular guidance, cyber threat updates, resources, toolkits and more. Find out more by using this link: Cyber Resilience Centre for Wales (wcrcentre.co.uk)
- What to do if your computer has been ‘hacked’: contact Action Fraud at www.actionfraud.police.uk where you can report fraud and cybercrime to police
- IPO’s IP Healthcheck is a suite of free online tools that will help you protect your intellectual property. It includes advise on keeping your IP safe: https://www.ipo.gov.uk/ip-support
To keep in touch, sign up to email updates from this blog, or follow us on Twitter.
Recent Comments